COLUMNS
Common Misconceptions About China's Corporate Espionage Tactics

Jun 18, 2019 | 10:00 GMT
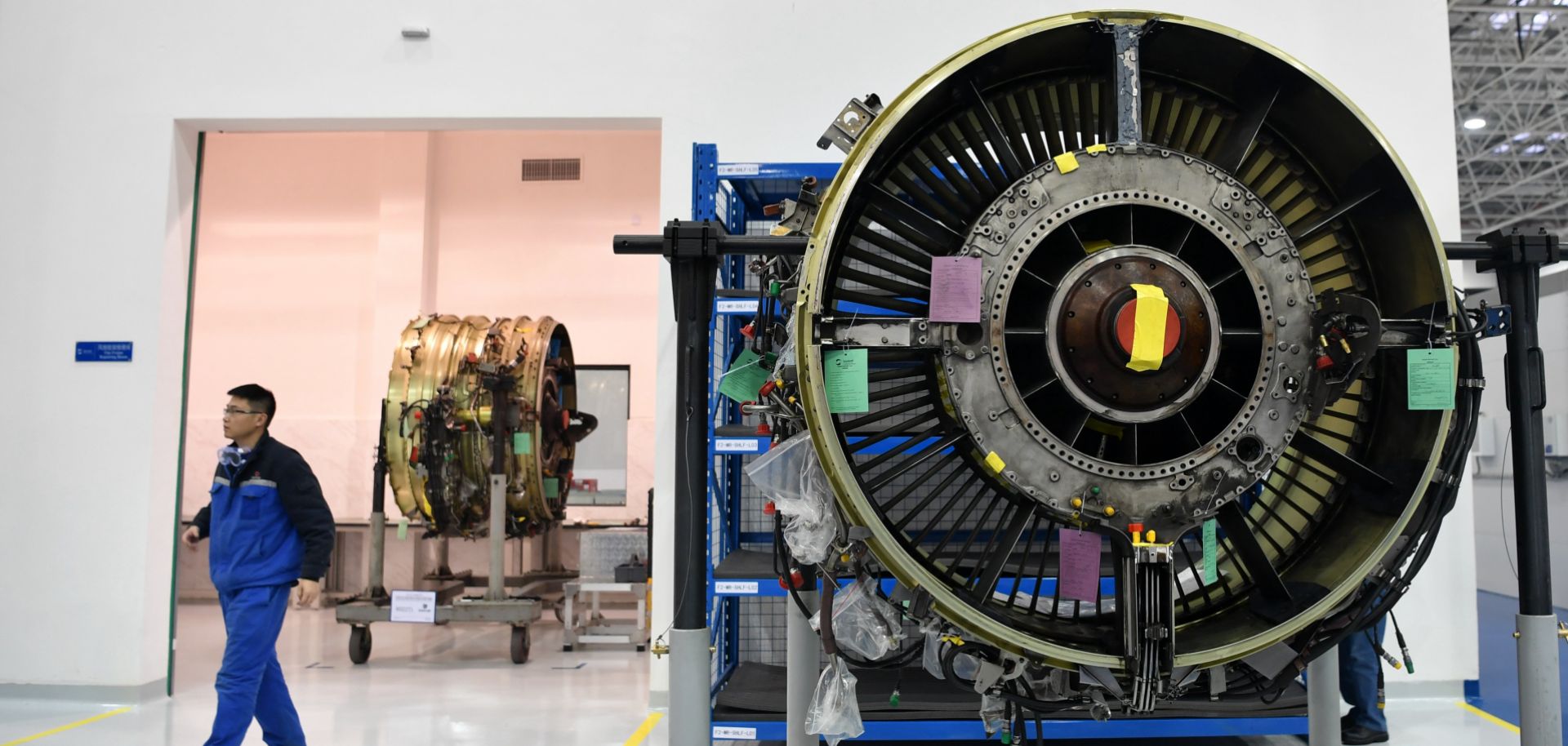
An aircraft engine undergoes maintenance at the aero-engine bonded maintenance base of Sichuan Services Aero-engine Maintenance Co., Ltd. (SSAMC) in Chengdu, China.
(Zhang Lang/Getty Images)
Highlights
- Several common misconceptions assume Chinese corporate espionage efforts are much more confined and predictable than they really are.
- This includes the dangerous belief that Beijing's intelligence agencies only recruit ethnic Chinese agents, or that they only recruit agents on their home turf in China.
- The Chinese government and state-owned entities also frequently benefit from walk-in agents who offer stolen information of their own accord.
- Thus, whether employees are at risk of providing trade secrets to Chinese intelligence actors should be evaluated purely on their behavior, and not on their ethnicity or location.
Subscribe Now
SubscribeAlready have an account?
