COLUMNS
In Countering a Creative Security Threat, Anticipation Is Key

Sep 17, 2019 | 09:00 GMT
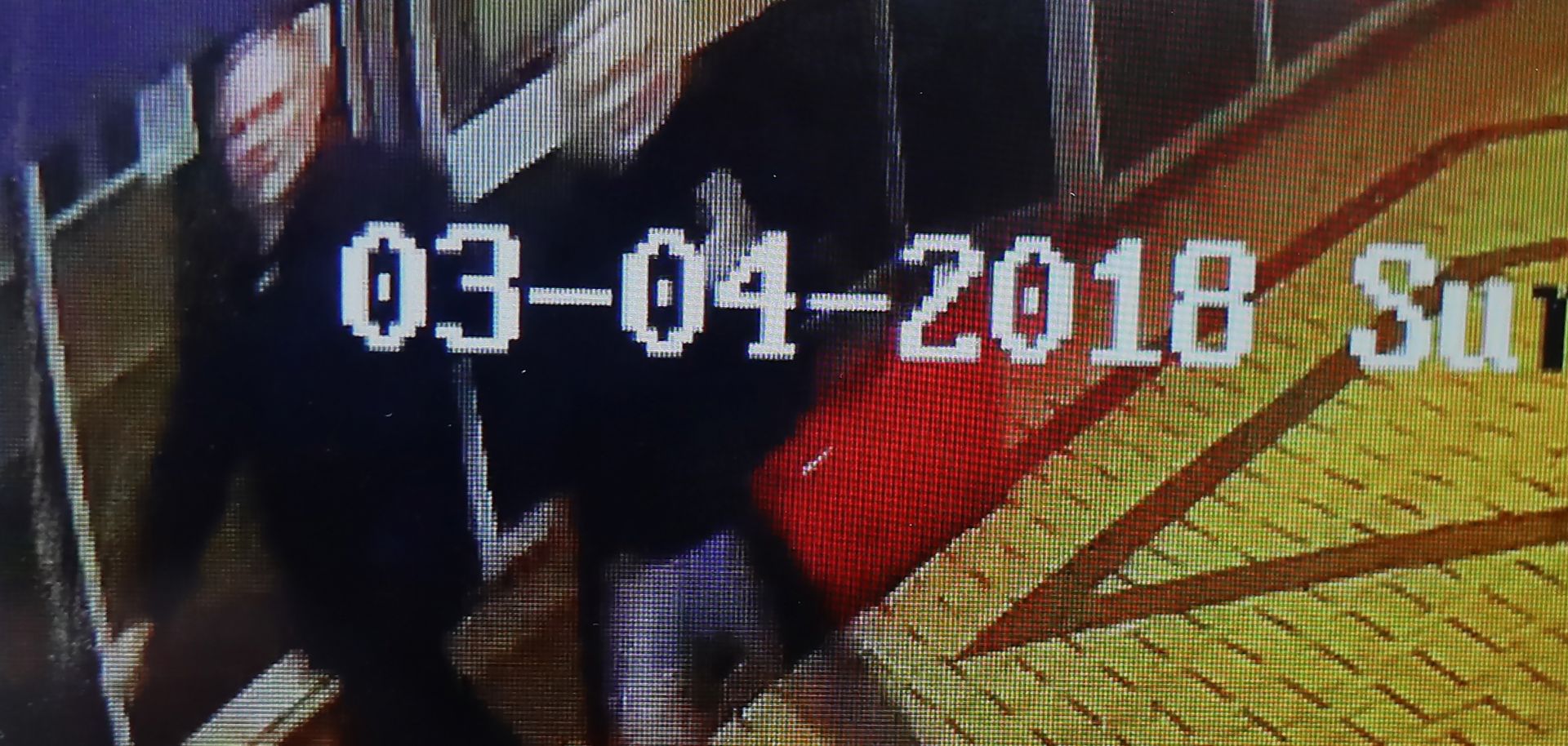
Closed circuit TV footage on a mobile phone is believed to show former Russian spy Sergei Skripal (left), and his daughter, Yulia Skripal, walking in the center of Salisbury, United Kingdom, not long before they were poisoned. With criminals and spies ever resourceful, security departments require more flexibility if they are to counter their adversaries.
(DAN KITWOOD/Getty Images)
Highlights
- Because criminals, militants, spies and the like are ever resourceful, security personnel must overcome some of their traditional inflexibility in addressing threats to their companies.
- Focusing on trends in criminal tradecraft will help departments identify and prepare for the threats they are likely to face.
- Security departments can nip a potential attack in the bud if they can deny resourceful adversaries the ability to conduct surveillance at will.
Subscribe Now
SubscribeAlready have an account?
