COLUMNS
North Korea's Hackers Play the Long Game

Sep 18, 2018 | 09:30 GMT
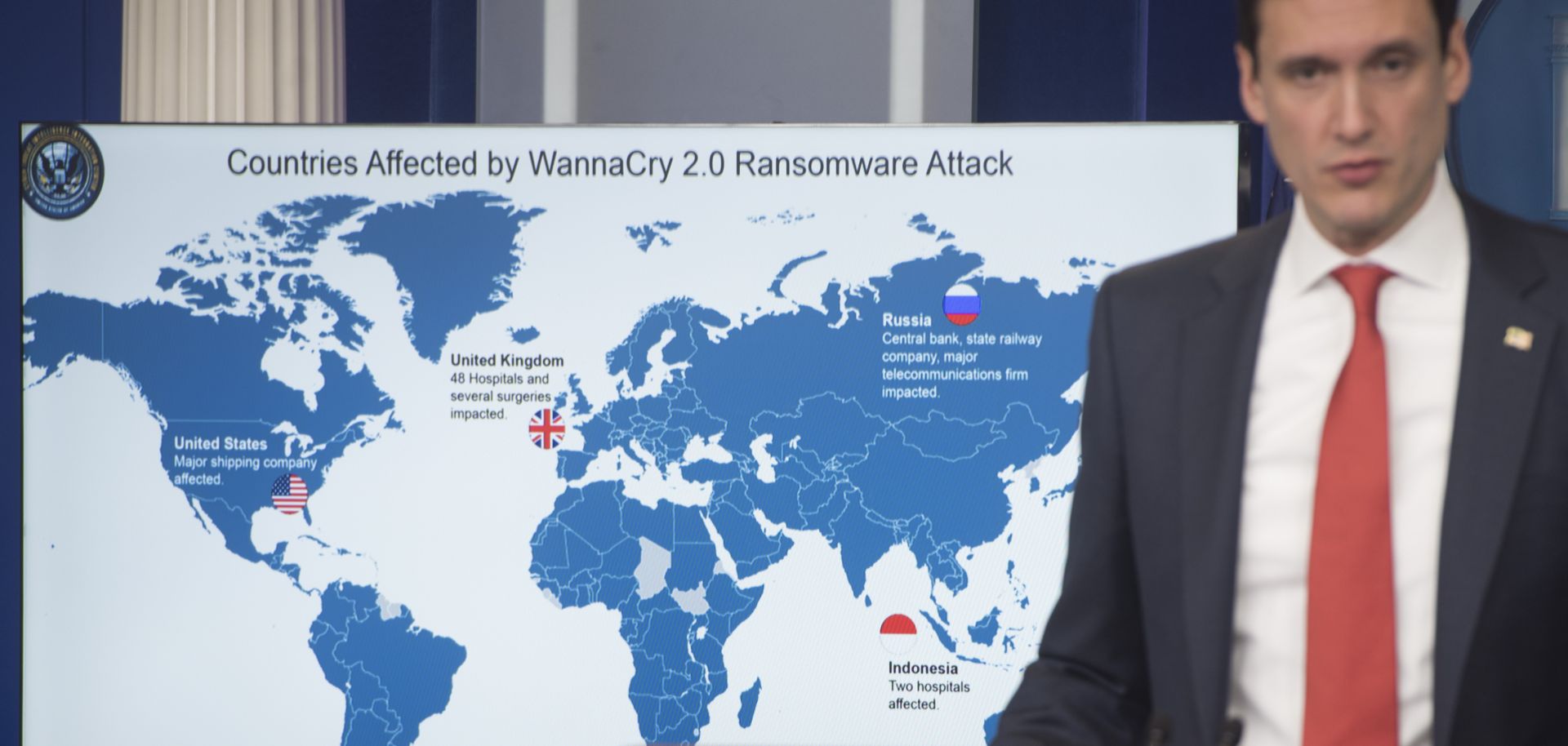
White House homeland security adviser Tom Bossert speaks about the WannaCry virus, which was tied to North Korea, during a briefing at the White House in Washington on Dec. 19, 2017. Pyongyang is generally meticulous in its planning for cyberattacks.
(SAUL LOEB/AFP/Getty Images)
Highlights
- A U.S. federal investigation has shown that Pyongyang has been planning its cyberattacks far in advance, typically with the aim of stealing money rather disrupting its enemies.
- North Korea and others rely on invasive surveillance to increase the potency of their attacks, yet such action increases the chances that hackers will be detected ahead of time.
- Investigations into hacking can force assailants to alter their tactics and operations, but they are not enough to stop them outright.
Subscribe Now
SubscribeAlready have an account?
