COLUMNS
Employees Can Be the Biggest Threat — and Asset — for Workplace Security Programs

Aug 13, 2019 | 09:00 GMT
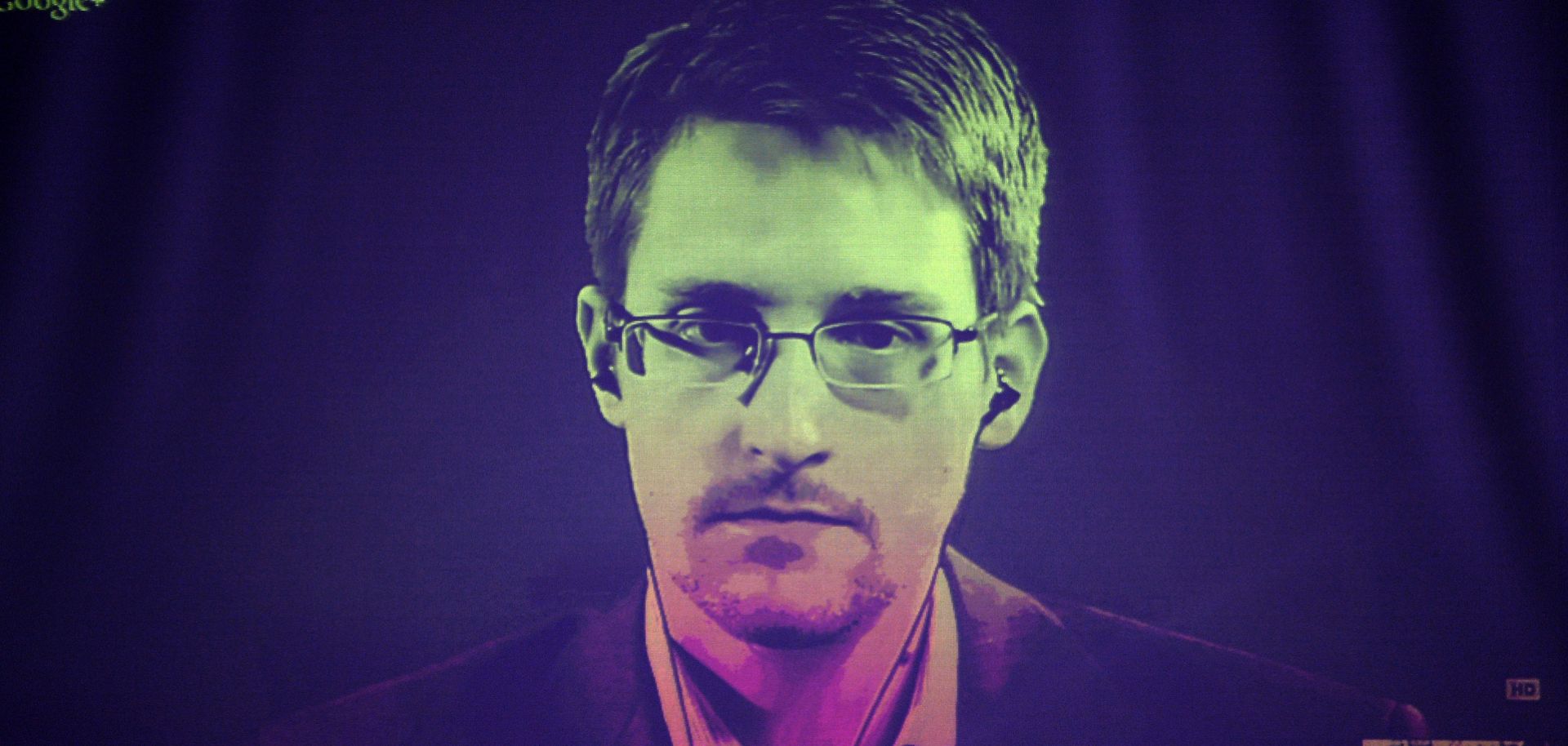
Insider threat actors can include current or former employees, contractors like Edward Snowden (pictured), service providers and business partners.
(FREDERICK FLORIN/AFP/Getty Images)
Highlights
- The intimate knowledge that insiders have of an organization's security programs, policies and procedures put them in a position to cause significant damage, whether by conducting an act of workplace violence, corporate espionage or another crime.
- Insider threat actors can include current employees, former employees, contractors, service providers or someone working for a business partner (such as a web-hosting service).
- While security teams may provide leadership on the issue, protecting against insider threats is really a corporatewide responsibility.
- It's not enough to continuously monitor employees; all staff members at an organization should also know how to recognize suspicious behaviors and who should be informed of them.
Subscribe Now
SubscribeAlready have an account?
