COLUMNS
A Sting Operation Lifts the Lid on Chinese Espionage

Oct 16, 2018 | 09:00 GMT
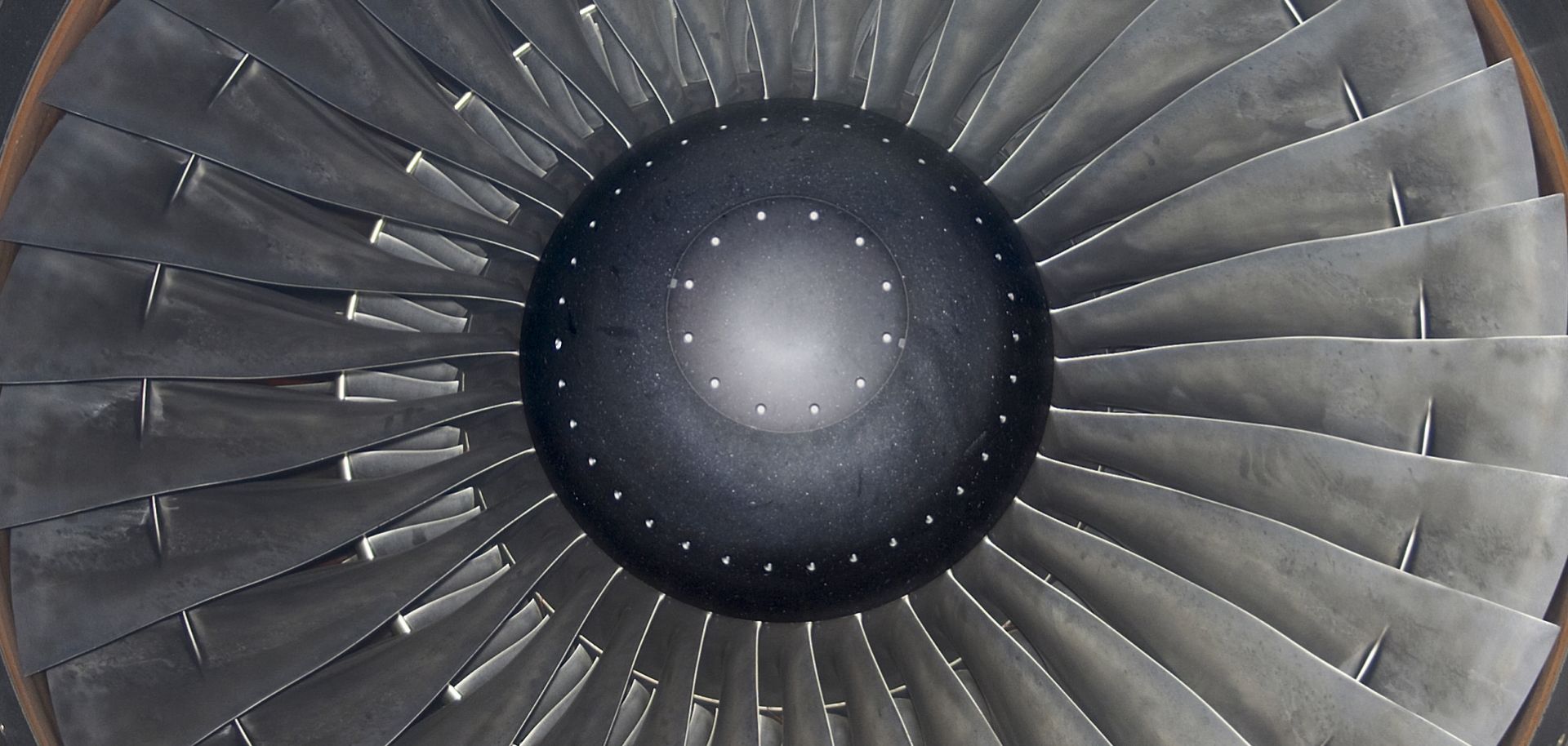
A jet engine is seen in this file photo. Chinese national Xu Yanjun is accused of attempting to steal jet technology from a company in the United States.
(MICHAEL WINSTON ROSA/Shutterstock.com)
Highlights
- China and others, such as Russia, will continue their attempts to acquire intelligence as they strive to achieve technological parity with the West.
- Because it is faster and cheaper to steal technology than develop it from scratch, Western companies, universities and other organizations will remain prime targets.
- Although the Chinese operative at the center of the latest case has been captured, the high stakes involved mean that the arrest will do little to curb the persistent threat of industrial espionage.
Subscribe Now
SubscribeAlready have an account?
