AssessmentsOct 13, 2021 | 21:20 GMT
What’s Next for Russia’s Crackdown on Big Tech?
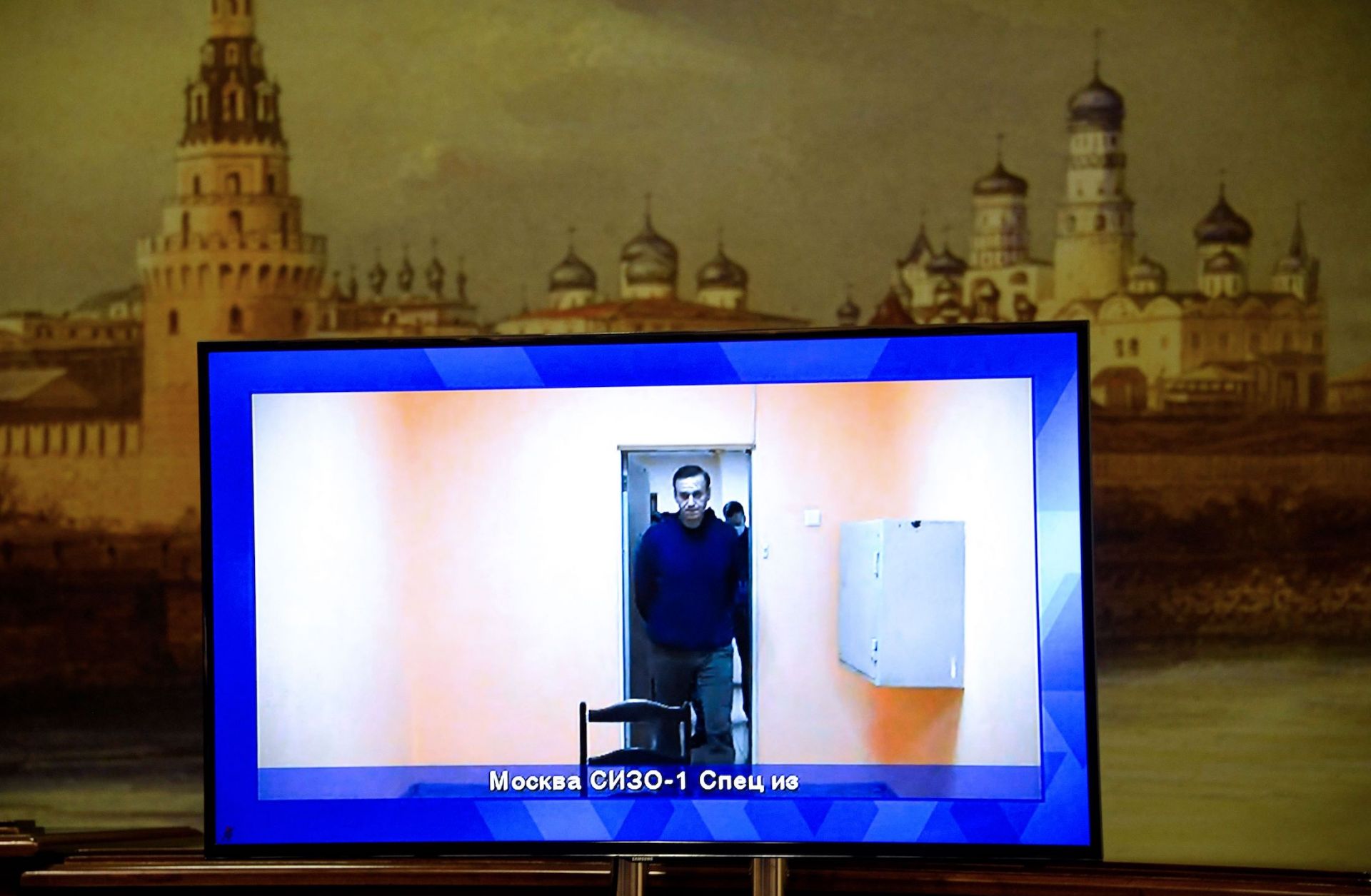
With parliamentary elections now behind it, the Russian government will maintain its pressure campaign against Big Tech, threatening companies to coerce them into compliance while diluting their influence with domestic analogs in the coming years. Last year, the Kremlin launched a crackdown on political dissent to prevent the September elections for the Russian State Duma from resulting in opposition victories or mass protests. As the crackdown sought to narrow permitted political speech and information accessible in Russia, one of the focal points of the campaign became U.S.-based “Big Tech” companies like Google, Apple, Facebook, Twitter and Amazon, as well as other smaller tech companies. Russian independent media and political activists rely on these platforms to spread their message and demand more democratic governance in Russia, which the regime views as a threat. Moscow envisions sufficiently pliable domestic entities -- such as Russia’s large tech conglomerates like Yandex, VK, and Sber
READ MORE